AMD has disclosed a high-severity vulnerability (CVE-2024-56161) in its Secure Encrypted Virtualization (SEV) technology, which could allow attackers with administrative…
Category: Vulnerability
A critical Cross-Site Scripting (XSS) vulnerability, tracked as CVE-2024-57004, has been discovered in Roundcube Webmail version 1.6.9. This flaw allows…
A significant security vulnerability has been discovered in Alibaba Cloud Object Storage Service (OSS), enabling unauthorized users to upload data…
A critical security vulnerability has been identified in TeamViewer Clients for Windows, allowing attackers with local access to escalate their…
A significant zero-day vulnerability in Zyxel CPE series devices, identified as CVE-2024-40891, is being actively exploited by attackers. This vulnerability…
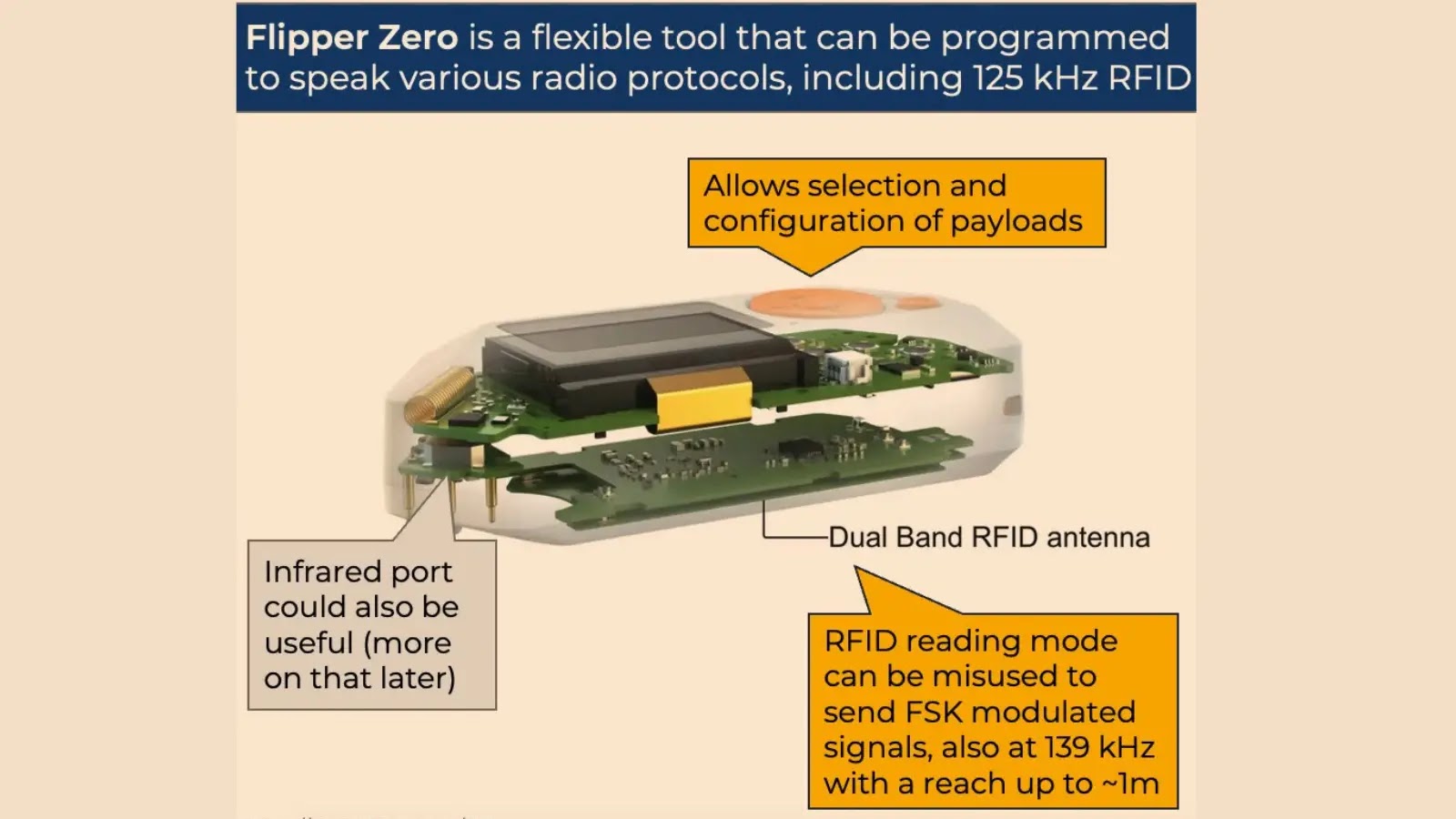
Researchers Fabian Bräunlein and Luca Melette demonstrated how outdated Radio Ripple Control systems, used to manage up to 60 gigawatts…
Vulnerability Assessment and Penetration Testing (VAPT) tools are an integral part of any cybersecurity toolkit, playing a critical role in…
U.S. Cybersecurity and Infrastructure Security Agency (CISA) issued six Industrial Control Systems (ICS) advisories to address significant vulnerabilities in critical…
Over 379 Ivanti Connect Secure (ICS) devices were found to be backdoored following the exploitation of a critical zero-day vulnerability,…
A critical vulnerability has been identified in Apache CXF, a widely used open-source framework for web services. This flaw, tracked…